Threat actors bypass security tools and use AI to launch faster ransomware attacks that exploit valid credentials and target data
Ransomware is not only growing; threat actors are accelerating the pace of their attacks by using offensive tools to exploit valid credentials and hit targets with speed and precision.
The practice has undergone big changes over the past five years. Initially, attacks focused on encrypting data; now, threat actors threaten to extract it to pressure victims into paying. Double-extortion tactics quickly shifted to triple-extortion threats to expose stolen data. Threat actors also transitioned from extorting companies to contacting victims directly — whatever it takes to rake in the cash.
The latest shift is all about speed. Ransomware actors discovered methods to bypass endpoint detection and response (EDR) tools, and they're increasingly using artificial intelligence (AI) to steal data more quickly.
Over the past 18 to 20 months, the prevalence of ransomware has increased, and attack quality has also improved, warns Mick Coady, field CTO of Elisity Cybersecurity. Attackers know that medical devices, especially those over five years old, can't be protected by EDRs, so they target them rather than patchable IT devices.
"At the end of the day, I think the sophistication has been more about them getting new angles of attack," Coady says.
Arctic Wolf found similar trends in its 2026 Threat Report: ransomware accounted for 44% of its incident response (IR) cases last year, and threat actors are operating at "increased speed and specialization." The report found that threat actors adapted to organizations' defenses by using automation to compress the kill chain and bypassed controls "by logging in, not breaking in."
That is the most striking shift from the recent year, says Kerri Shafer-Page, vice president of digital forensics and IR at Arctic Wolf. Threat actors are still getting in through the perimeter by exploiting vulnerabilities in firewalls and VPNs, but they're also using valid credentials.
Access management contributes to major hygiene issues, Shafer-Page observes. Too many individuals within a company hold over-privileged identities, and once threat actors gain that privileged access, they "break all the store windows" as they move laterally to take everything and quickly leave.
The use of offensive security tools is one of the biggest shifts for ransomware gangs, agrees Will Thomas, senior threat intelligence advisor at Team Cymru. Many of the initial access vectors for ransomware have shifted from malware loaders and botnets to exploiting devices, phishing, brute-force attacks, and infostealers.
As companies race to adopt AI, so do attackers. Arctic Wolf noticed threat actors using AI to conduct vulnerability and general research on victim organizations.
Attackers are leveraging AI in two primary ways: scaling and automation, and high-fidelity social engineering tactics, says Matt Hull, vice president of cyber intelligence and response at NCC Group. NCC Group recorded a staggering 50% year-on-year increase in global ransomware attacks in 2025.
AI-advanced tooling has effectively lowered the barrier to entry for cybercrime. Now, less technical threat actors can conduct sophisticated ransomware campaigns at scale. NCC Group also saw a rise in real-time deepfake vishing, used to bypass traditional verification protocols by impersonating trusted executives or colleagues.
Organizations are struggling to defend against the latest evolution of ransomware, due in part to an increasingly decentralized ecosystem. What used to be a handful of larger loader botnets and ransomware-as-a-service campaigns is now extending exponentially.
Law enforcement actions knocked LockBit 3.0 off the top charts, and Qilin emerged as the "apex predator." Qilin's prominent reputation is even drawing impersonators — Arctic Wolf handled one IR case where a threat group was posing as Qilin, having somehow gotten onto their leak site to post a victim's name.
"When we followed through with that actual threat group who owned all of that territory, they were like: 'We don't know what you're talking about. We have no issue with that client.' And they removed them from their leak site," Shafer-Page reveals.
To address ransomware's ongoing evolution, Shafer-Page urges organizations to:
It's increasingly important to take steps to combat ransomware, since it doesn't seem to be going anywhere. Data extortion in particular is expected to rise significantly.
Source: Dark Reading
Ransomware is not only growing; threat actors are accelerating the pace of their attacks by using offensive tools to exploit valid credentials and hit targets with speed and precision.
The practice has undergone big changes over the past five years. Initially, attacks focused on encrypting data; now, threat actors threaten to extract it to pressure victims into paying. Double-extortion tactics quickly shifted to triple-extortion threats to expose stolen data. Threat actors also transitioned from extorting companies to contacting victims directly — whatever it takes to rake in the cash.
The latest shift is all about speed. Ransomware actors discovered methods to bypass endpoint detection and response (EDR) tools, and they're increasingly using artificial intelligence (AI) to steal data more quickly.
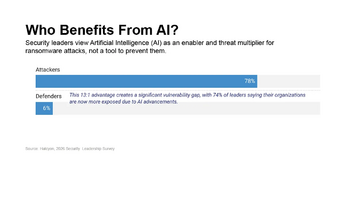
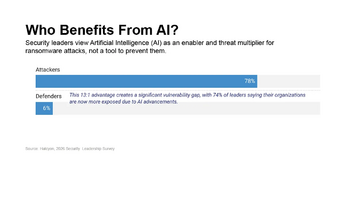
Halycon's 2026 Method Survey Report revealed that while 98% of organizations use EDR for ransomware defense, only 25% "actually trust it to defend against today's evolving ransomware threat." Additionally, 78% of surveyed participants said AI made ransomware attacks more effective. Conversely, only 6% believe the tools have improved their own defenses.
Over the past 18 to 20 months, the prevalence of ransomware has increased, and attack quality has also improved, warns Mick Coady, field CTO of Elisity Cybersecurity. Attackers know that medical devices, especially those over five years old, can't be protected by EDRs, so they target them rather than patchable IT devices.
"At the end of the day, I think the sophistication has been more about them getting new angles of attack," Coady says.
Living-Off-the-Land Techniques Continue
Arctic Wolf found similar trends in its 2026 Threat Report: ransomware accounted for 44% of its incident response (IR) cases last year, and threat actors are operating at "increased speed and specialization." The report found that threat actors adapted to organizations' defenses by using automation to compress the kill chain and bypassed controls "by logging in, not breaking in."
That is the most striking shift from the recent year, says Kerri Shafer-Page, vice president of digital forensics and IR at Arctic Wolf. Threat actors are still getting in through the perimeter by exploiting vulnerabilities in firewalls and VPNs, but they're also using valid credentials.
Kerri Shafer-Page said:It's challenging to keep the employee base educated. It has to be a drumbeat because of attackers' sophistication.
Access management contributes to major hygiene issues, Shafer-Page observes. Too many individuals within a company hold over-privileged identities, and once threat actors gain that privileged access, they "break all the store windows" as they move laterally to take everything and quickly leave.
The use of offensive security tools is one of the biggest shifts for ransomware gangs, agrees Will Thomas, senior threat intelligence advisor at Team Cymru. Many of the initial access vectors for ransomware have shifted from malware loaders and botnets to exploiting devices, phishing, brute-force attacks, and infostealers.
Will Thomas said:Infostealers just need one infection, and you get the credentials and log in, compared to loader botnets that need to maintain persistence and to remain undetected. If you can just get credentials, then you can just log in.
AI Is Leading to Higher Quality Attacks
As companies race to adopt AI, so do attackers. Arctic Wolf noticed threat actors using AI to conduct vulnerability and general research on victim organizations.
Attackers are leveraging AI in two primary ways: scaling and automation, and high-fidelity social engineering tactics, says Matt Hull, vice president of cyber intelligence and response at NCC Group. NCC Group recorded a staggering 50% year-on-year increase in global ransomware attacks in 2025.
AI-advanced tooling has effectively lowered the barrier to entry for cybercrime. Now, less technical threat actors can conduct sophisticated ransomware campaigns at scale. NCC Group also saw a rise in real-time deepfake vishing, used to bypass traditional verification protocols by impersonating trusted executives or colleagues.
What Does it Look Like on the Defensive Side?
Organizations are struggling to defend against the latest evolution of ransomware, due in part to an increasingly decentralized ecosystem. What used to be a handful of larger loader botnets and ransomware-as-a-service campaigns is now extending exponentially.
Will Thomas said:It's scary how simple it can be because all these tools and guides are available out there.
Law enforcement actions knocked LockBit 3.0 off the top charts, and Qilin emerged as the "apex predator." Qilin's prominent reputation is even drawing impersonators — Arctic Wolf handled one IR case where a threat group was posing as Qilin, having somehow gotten onto their leak site to post a victim's name.
"When we followed through with that actual threat group who owned all of that territory, they were like: 'We don't know what you're talking about. We have no issue with that client.' And they removed them from their leak site," Shafer-Page reveals.
How to Respond
To address ransomware's ongoing evolution, Shafer-Page urges organizations to:
- Be upfront and transparent with CISOs and the board
- Have meaningful conversations with budget decision-makers
- Maintain a clear picture of where all data is stored
- Control access management, especially for smaller IT shops
It's increasingly important to take steps to combat ransomware, since it doesn't seem to be going anywhere. Data extortion in particular is expected to rise significantly.
Kerri Shafer-Page said:When you and I talk to each other again next year, I'll start with the same thing: 'Yes, ransomware is Number One.'
Source: Dark Reading